
Quantum Noise Ciphertext Masking
Background
When we send sensitive data over the public network, we rely on encryption for confidentiality. The data is transformed into a ciphertext before being transmitted to the intended recipient.
During transmission, an attacker can intercept and make a copy of the ciphertext. Even if the attacker cannot decrypt the ciphertext immediately, the ciphertext can be stored and the attacker can come back in the future to attempt decryption using more powerful computers or more advanced cryptanalytic techniques.
Technology
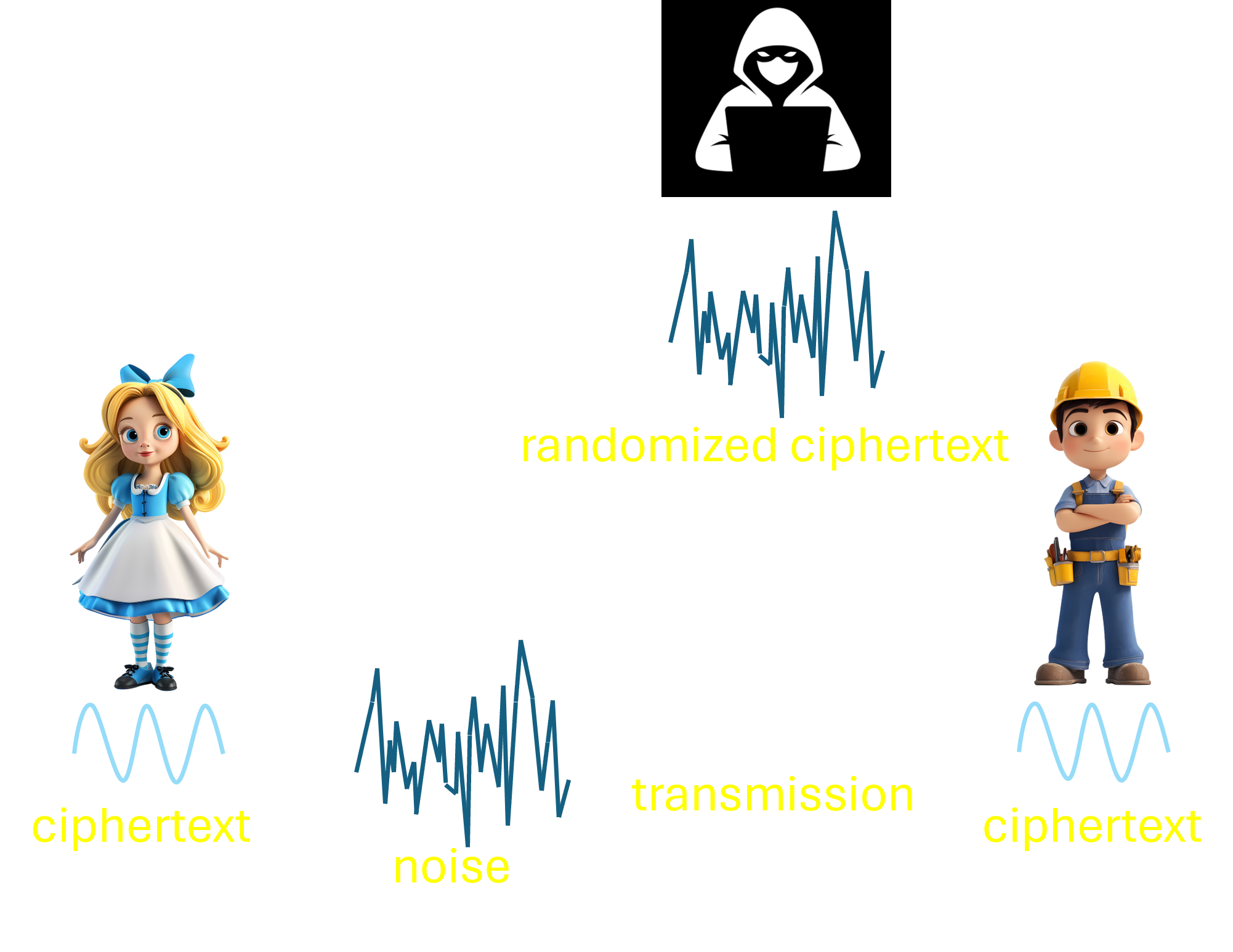
Ciphertext masking aims to prevent the ciphertext from being copied by an attacker. Here is how it works.
Alice first encodes her ciphertext using a secret key in a way that the ciphertext becomes embedded in noise. She then transmits this to Bob, who decodes using the same secret key. After decoding, Bob recovers the clean ciphertext from the noise. An attacker who does not know the secret key can only obtain a randomized version of the ciphertext.
We use the inherently noisy fluctuation of laser light to mask the ciphertext. Unlike classical noise, this laser noise, also known as shot noise, is due to the fundamental quantum nature of light and therefore cannot be predicted or manipulated by anyone.
Quantum computers
Product
The DenseKey Transceiver implements Quantum Noise Ciphertext Masking. It supports a data rate of 1.25 Gbps and a transmission distance of 200 km over optical fiber. It is plug-and-play and compatible with conventional cryptographic schemes such as AES.
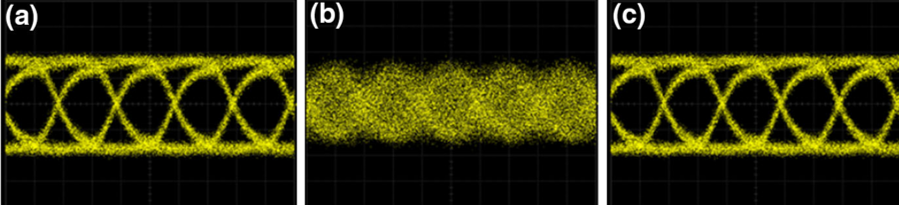
The figure on the right shows optical signals (a) before masking, (b) after masking, and (c) after unmasking. An attacker can only see the masked ciphertext, while the intended recipient can recover the clean ciphertext after unmasking.


Contact Us
sales@densekey.com